I was troubleshooting a Cisco WLC configured as FlexConnect (or H-REAP) to a remote AP 1242 that wouldn't join. You can view WLC logs under Management > Logs > Message Logs.
*spamApTask2: Aug 26 13:37:28.876:
#DTLS-3-HANDSHAKE_FAILURE: openssl_dtls.c:681 Failed to complete DTLS handshake
with peer 192.168.10.14 for AP d4:6d:50:88:12:34
*spamApTask3: Aug 26
13:36:13.824: #DTLS-3-HANDSHAKE_FAILURE: openssl_dtls.c:681 Failed to complete
DTLS handshake with peer 192.168.10.14 for AP d4:6d:50:88:12:34
*spamApTask2: Aug 26
13:35:03.936: #DTLS-3-HANDSHAKE_FAILURE: openssl_dtls.c:681 Failed to complete
DTLS handshake with peer 192.168.10.14 for AP d4:6d:50:88:12:34
<OUTPUT TRUNCATED>
(Cisco Controller)
>show ap join stats summary all
Number of
APs.............................................. 1
Base Mac AP EthernetMac AP Name IP Address Status
00:3a:99:12:ab:cd
58:8d:09:03:12:34 ap01 192.168.10.14 Not Joined
Since DTLS need accurate date and time, I tried to manually configure the WLC date/time, timezone under Commands > Set Time and also removed NTP but still no joy.
I also tried to upgrade the WLC AireOS 7.4.121.0 > 7.4.150.0 but still AP won't join the WLC.
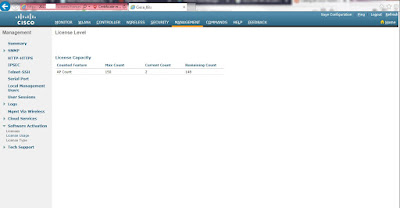
My search led me to an expired WLC Manufacturer Installed Certificate (MIC) which has reached its 10 year expiration date. Below are some WLC commands as a workaround.
(Cisco Controller)
>config ap ?
802.1Xuser Configures the dot1x user for AP.
SSH Enables/Disables SSH.
add Adds a Foreign Access Point.
bhrate Configures Cisco Bridge Backhaul Tx
Rate.
bridgegroupname
Sets/Deletes bridge group name.
bridging Enables/Disables Ethernet-to-Ethernet
bridging.
cdp Enable/Disable CDP on Cisco AP.
cert-expiry-ignore
Configures cert-expiry-ignore check operation.
core-dump Configures the AP's memory core dump.
country Configures the country of operation.
crash-file Manages crash data and radio core files.
delete Deletes a Foreign Access Point.
disable Disables Cisco APs
enable Enables Cisco APs
ethernet Configures Ethernet Port of the AP
flexconnect Enables/Disables VLAN on the flexconnect.
group-name Configures the group name.
hotspot Configures Hotspot configs on the AP.
image Configure image.
led-state Enables/Disables the LED-State or
configure LED flash
link-encryption
Capwap Data Link encryption options
--More-- or (q)uit
link-latency Configures Link Latency Feature.
location Configures the Location.
logging Configures the AP logging.
mgmtuser Configures the user for AP management.
mode Configures an AP's mode of operation.
monitor-mode Configures an AP's monitor-mode channel
optimization.
name Configures the Name of an AP.
packet-dump Configure AP Packet Capture parameters
port Configures the port for a Foreign
Access Point.
power Configures Cisco Power over Ethernet
(PoE) feature for an AP
primary-base Configures the Primary Cisco Switch for an
AP.
priority Configure the AP's priority.
reporting-period
Configures the AP's rogue/error reporting period
reset Resets an AP
retransmit Configures AP Control packet
retransmission parameters.
role Configures an AP's Bridge role of operation.
rst-button Enables or disables the Reset Button.
secondary-base
Configures the Secondary Cisco Switch for an AP.
sniff Enables/Disables sniffing on a radio.
static-IP Enables/Disables/Changes an AP's static
IP address configuration
stats-mode Configures the mode(realtime vs normal) in
which statistics are sent from an AP
stats-timer Configures the frequency at which
statistics are sent from an AP
syslog Configures the system logging settings
for an AP
--More-- or (q)uit
tcp-mss-adjust
Configures TCP on Cisco AP.
telnet Enables/Disables telnet.
tertiary-base Configures the Tertiary Cisco Switch for an
AP.
tftp-downgrade
Initiates AP's image downgrade from a TFTP server
(Cisco Controller)
>config ap cert-expiry-ignore ?
mic Configures cert-expiry-ignore check
operation for MIC.
ssc Configures cert-expiry-ignore check
operation for SSC.
(Cisco Controller)
>config ap cert-expiry-ignore mic ?
enable Enabling will ignore the
lifetime-check for MIC.
disable Disabling will do the lifetime-check
for MIC.
(Cisco Controller)
>config ap cert-expiry-ignore mic enable
(Cisco Controller)
>config ap cert-expiry-ignore ssc ?
enable Enabling will ignore the
lifetime-check for SSC.
disable Disabling will do the lifetime-check
for SSC.
(Cisco Controller)
>config ap cert-expiry-ignore ssc enable
(Cisco Controller)
>config auth-list ?
add Creates an authorized AP entry.
ap-policy Configures an AP authorization policy.
delete Delete an existing AP entry.
(Cisco Controller)
>config auth-list ap-policy ?
authorize-ap Configures AP authorization policies.
authorize-lsc-ap Use
auth-list to Authorize APs with Locally Significant Certificate.
ssc Configures authorization of APs
with self-signed certificate.
mic Configures authorization of APs
with manufacturing-installed certificates.
lsc Configures authorization of APs
with locally significant certificates.
(Cisco Controller)
>config auth-list ap-policy ssc ?
enable Allows APs with self-signed
certificates to connect.
disable Disallows APs with self-signed
certificates to connect.
(Cisco Controller)
>config auth-list ap-policy ssc enable
(Cisco Controller)
>config certificate ?
compatibility Configure certificate compatibility mode.
generate Generates new certificates.
lsc Configure Locally Significant
Certificates (LSC)
ssc Configure Self Signed Certificates
(SSC)
use-device-certificate
Use device certificate.
(Cisco Controller)
>config certificate ssc ?
hash Configure Self Signed Certificates
hash
(Cisco Controller)
>config certificate ssc hash ?
validation Configures validation of SSC Hash
(Cisco Controller)
>config certificate ssc hash validation ?
enable Enable hash validation of SSC
certificate
disable Disable hash validation of SSC
certificate
(Cisco Controller)
>config certificate ssc hash validation
enable
(Cisco Controller)
>save config
Are you sure you
want to save? (y/n) y
Configuration Saved!
After the said commands were configured, the AP 1242 joined the WLC again.
(Cisco Controller)
>show ap join stats summary all
Number of
APs.............................................. 1
Base Mac AP EthernetMac AP Name IP Address Status
00:3a:99:12:ab:cd
58:8d:09:03:12:34 ap01 192.168.10.14 Joined